Upskill Your Workforce to Fill Cybersecurity Roles
You likely already know that cybercrimes are on the rise, and they’re getting more sophisticated and more plentiful every year. The FBI reports an average of 300,000 complaints per year; that’s over 800 a day.
- Number of complaints filed with the FBI annually:
- 2014—269,442
- 2015—288,012
- 2016—298,728
- 2017—301,580
- 2018—351,937
- Estimated annual losses, according to the FBI:
- 2014—$800.5 million
- 2015—$1 billion
- 2016—$1.4 billion
- 2017—$1.4 billion
- 2018—$2.7 billion
In its report “2018 Trends in Cybersecurity: Building Effective Security Teams,” tech industry thought leader CompTIA identified three industry trends:
- Digital real estate is growing. As our digital infrastructure grows, so does the “attack surface”; in other words, the more digital real estate we acquire, the bigger targets we become.
- The need for cyber skills is outpacing basic skills. Employers and all of their employees, not just IT teams, lack cybersecurity knowledge and training.
- Stronger metrics are needed to quantify cybersecurity efforts and success. As information security moves toward proactivity, we need better metrics to measure successes and/or justify a greater investment.
To illustrate how sophisticated cyberattacks have become, look at data reported by the Identity Theft Resource Center (ITRC) in its 2018 End-of-Year Data Breach Report. They found that while there was a decrease in the number of attacks from 2017 to 2018, the number of affected records increased by 126%. This suggests that while cybercriminals may have breached fewer organizations, they may be getting better at targeting organizations with bigger databases.
| ITRC End-of-Year Data Breach Report | 2017 | 2018 |
|---|---|---|
| Total Incidents | 1,632 | 1,244 |
| Records Exposed | 197,612,748 | 446,515,334 |
Next, we’ll explore five ways cybercriminals target businesses, as well as how you can upskill your cybersecurity workforce to protect your most valuable digital assets.
5 Types of Cyberthreats to Businesses
Cyberattacks come in many forms and through many attack channels , whether it’s through email, web traffic, smartphone applications, or any other digital channel. Here are five common types of attacks, some of which overlap with each other.
1. Phishing and Pharming
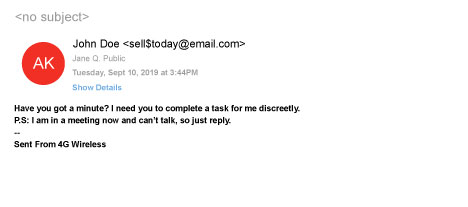
Company emails are especially vulnerable to phishing schemes, and the architects behind them are very good at spoofing messages. They use highly recognizable brands (Microsoft, PayPal, Chase) and design email messages with the companies’ branding and urgent messages to take action or face a negative consequence.
Phishing happens when a cybercriminal tries to trick individuals into turning over personal information or giving them access to computers, servers, and online accounts. They install malware, worms, ransomware, and viruses that can corrupt data or give them access to financial and personal information.
Pharming targets your website address, or domain name system (DNS), by hijacking it and redirecting visitors to a spoofed website (see No. 5 on this list). The users think they’re interacting with a familiar brand, but they’re actually interacting with an imposter. Banks are especially vulnerable to pharming schemes.
Any busy employee could easily fall for one of these scams, click a link, and allow malware or ransomware to infiltrate your digital business.
2. Social Engineering
Phishing and pharming are forms of social engineering, but there are other, even more sophisticated ways that cybercriminals target victims. Social engineering scams often involve customer service and tech support from brands you recognize and use.
In one notorious social engineering scam, cybercriminals created fake Facebook customer support pages, so that when Facebook users searched for “Facebook customer service,” imposter websites would show up. The unsuspecting Facebook users would dial what looks like a toll-free number and speak to a friendly and “helpful” customer service rep who, for a fee, will fix their problems. Red flag warning: The customer service fee had to be paid in gift cards “to protect customers from anyone getting hold of their credit card numbers.”
3. Credential Harvesting
While credential harvesting is often referred to as a form of phishing, it’s not only through email that criminals try to get personal identification information and access to accounts. It can also happen at the hardware level, where criminals use sophisticated technology to steal information from point-of-sale systems, ATMs, and gas pumps, for example. To protect themselves and their customers, more companies are using multi-factor account authentication and biometrics, as well as cybersecurity upskilling and education (more on that in the next section) to protect themselves and their customers.
4. Ransomware Attacks
In its 2019 Internet Security Threat Report, cybersecurity software company Symantec said ransomware incidents against consumers declined for the first time since 2013; however, they’re up 20% for enterprises. Again, the data suggests that cybercriminals are getting better at hyper-targeting organizations that generate the biggest payoffs. They’re shifting away from individuals and toward big targets with weak systems.
In 2018 and 2019, several ransomware attacks on local governments made headlines:
- Ransomware held 23 Texas cities hostage, affecting their online systems and email accounts.
- Lake City, Florida, paid attackers $460,000 for a decryption key to unlock servers that had been hijacked by ransomware.
- Riviera Beach, Florida, paid $600,000 to release ransomware.
Why do these governments pay? In many cases, it’s cheaper to pay the ransom than it is to replace the hardware and software.
5. DNS Hijacking and Spoofing
We’ve mentioned DNS hijacking and spoofing as a tactic that cyber pharmers use to trick customers into thinking they’re interacting with a bank, retailer, or tech support. Cybersecurity guru KrebsOnSecurity refers to it as DNSpionage and explains it like this: Cybercriminals steal email and login information from large databases and redirect internet traffic to an address controlled by the criminals.
Every web address has a user-friendly name and a numeric internet protocol (IP) address. Using sophisticated technology, perpetrators hijack the IP address and redirect traffic to their own web pages, and most users don’t notice because many people don’t look at the URL to ensure they’re at the right location.
Phishing, pharming, social engineering, credential harvesting, and DNS hijacking are only a few of the more common cyberthreats. There are more, but the point here is to help you understand how you can protect your workforce—and therefore your digital assets—against cyberattacks.
Cybersecurity Talent Gap
The growing demand for Cybersecurity workers is greater than the average demand across all jobs that the Bureau of Labor Statistics tracks. U.S. employers in the public and private sectors posted more than 313,000 job openings for cybersecurity workers between September 2017 and August 2018, according to the National Institute of Standards and Technology. The ratio of existing cybersecurity workers to the number of cybersecurity job openings is two to three.
Between now and 2022, the U.S. will have an estimated 3.5 million cybersecurity jobs to fill, according to Cybersecurity Ventures, a cybersecurity think tank and online magazine. The most in-demand positions are:
- IT security specialists
- Information security analysts
- Network security engineers
- Security engineers
- Software security engineers
Meanwhile, corporations, municipalities, and other organizations are looking for ways to educate their existing IT teams and non-IT professionals on cybersecurity.
For example, ManTech, a government defense contractor based in Virginia, partnered with Purdue Global to develop a customized training program to upskill its workforce. Their employees have access to a three-course training program that can help them qualify to sit for the Certified Information Systems Security Professional (CISSP) certification examination, which would help ManTech bid on government contracts.*
This is just one example of how a partnership with an accredited and highly respected university enables organizations to upskill their workforces and fill cybersecurity gaps. Purdue Global offers enterprise learning opportunities in various forms:
- Personal development programs to train employees for leadership positions
- Single-course training to help employees hone existing skills and learn new ones
- Course bundles that train workers to take on new roles and responsibilities and earn certificates of completion
- Specialized degree programs in health care, business, IT, and more
- ExcelTrack® degree programs to help employees earn bachelor’s and master’s degrees
Future of Cybersecurity
The need to upskill your cybersecurity workforce is clear. By 2021, cybercrime damages will reach approximately $6 trillion, according to cybersecurityventures.com.
If you need more reasons for upskilling your cybersecurity workforce, consider this:
- Artificial intelligence (AI) has a significant impact on technology and cybersecurity: An estimated 66% of organizations post-2019 (up from 20% of organizations pre-2019) are adopting AI, according to Capgemini Research Institute. AI isn’t expected to replace workers as much as it’s expected to enhance and change the way they work. In order to keep up with and protect their organizations, these companies are spending more to train their workforces in AI.
- The end of passwords is near, say many experts, including CSOOnline, a web-based magazine for security executives. The future of user access to secure banking, shopping, and other personal information is in AI-based systems such as biometrics.
Train your workforce because it benefits your organization by reducing recruitment costs and helps retain valuable institutional knowledge. Plus, today’s workforce wants and expects ongoing training to keep up with changes in the workplace. In a Pew survey, 54% of surveyed working adults said that to keep up with changes at work, they’ll need ongoing training throughout their careers.
In-Demand Cybersecurity Skills
Cybersecurity skills can be broken into three areas: hard skills, soft skills, and cyber security-specific skills.
Hard skills include risk management, software development, systems architecture, data administration, and compliance management.
Soft skills refer to leadership readiness, communication skills (written and verbal), relationship management, and critical thinking, especially in response to crises and crises prevention.
Cybersecurity-specific skills include:
- Coding and computer languages (Python, C/C++, and Java)
- Computer forensics
- Information and network security
- Information systems
- Intrusion detection and prevention
- Malware analysis and reverse engineering
- Operating systems (Apple, Linux, Microsoft Windows for example)
- Threat analysis
How to Train Your Workforce in Cybersecurity
The best way to upskill your workforce to fill cybersecurity roles is to partner with an organization that already has the curriculum to educate and train your first responders, managers, and general workforce.
Purdue Global has partnered with enterprises to create personalized training programs that target organizations’ specific needs. Our enterprise partners include government contractors, health care organizations, restaurants, retailers, and financial institutions.
Online cybersecurity training could range from a simple anti-hacking course to CISSP certifications to full bachelor’s and master’s degrees. Your employees can complete the coursework, certificate, and degree programs while incurring little to no out-of-pocket tuition or debt.†
Read more about our corporate training and education programs for cybersecurity. Or, if you’re ready to speak with a corporate education specialist, get in touch today.